Node.js Secure Coding:
Defending Against Command Injection Vulnerabilities
$ npm install static-server simple-git moment-timezone added 20 packages, and audited 21 packages in 4s 6 high severity vulnerabilities Don't take security vulnerabilities for granted. Learn how to write secure code.
Digital book
PDF & EPUBThe book features:
- 106 Pages
- 12 Vulnerable npm Packages
- 33 Self-assessment Questions
- 10 Chapters
- Light Mode
- Dark Mode SPECIAL EDITION
- July 2023 release
- Sale 15% OFF
Tip:
get 2 secure coding books bundle for $120.96 and save 30%
Buy Bundle



















 +400
+400
Join 460+ developers writing secure Node.js code
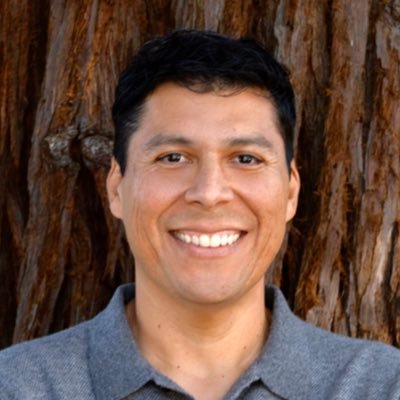
Quick peak into secure best practices and vulnerable code analysis
Handful of pages from the Node.js security book showing Command Injection vulnerabilities and Secure Coding flaws
of Downloads
Millions of for vulnerable open-source npm packages and projects reviewed in this book, demonstrating the wide impact on the ecosystem.
Chapters
2 introductory chapters, 6 CVE-focused chapters reviewing real-world vulnerable npm packages, 1 best practice chapter and 1 concluding in-the-wild vulnerabilities review chapter.
CVE Years
This book reviews up-to-date security vulnerabilities from the recent years, ranging from 2018 to 2022.
QUIZ Questions
Yes-no, Fill-the-blanks, and multiple answers questions to help you evaluate and test your knowledge in Node.js secure coding
Pages
Extensive hands-on exercises and practical code review of vulnerable code to draw insights and lessons learned
vulnerable npm packages
6 CVE chapters deeply reviewing vulnerable npm packages for lessons learned on command injection vulnerabilities, and 6 more references to vulnerable npm packages to exercise your secure coding skills.
Leading Developers Practice Node.js Secure Coding
Read testimonials by leading developers who took the training and leveled-up their skills to practice Node.js Secure Coding
"I have finished reading Node.js Secure Coding from Liran Tal. I read the whole thing in an hour without realizing it. I learned and discovered a few things along the way. I laughed at the IFS, didn't see it coming."

Thomas Gentilhomme
Node.js lead at MyUnisoft, Node Security WG
"Liran Tal, your book on Node.js security is an absolute gem! The abundance of real-world examples with commented fixes is incredibly valuable. Your practical solutions have enlightened me, especially the discovery of the shell-quote module! Recommended to all Node.js developers!"

Manuel Spigolon
Senior Software Developer at NearForm
"I wholeheartedly enjoyed working and learning from Liran's expertise in securing applications. With extensive experience speaking at global conferences and actively contributing code to the community, he is a true authority in the field. I highly endorse both his enlightening book and engaging workshop, as they are invaluable resources for anyone looking to enhance their understanding and implementation of application security"

Yoni Goldberg
Software Architect, Node.js Specialist
"Liran Tal just published a new book about Node.js secure coding. It is worth taking a look at!"

Daniel Garcia
Cybersecurity & API Security Consultant
"I highly recommend the new Node.js Secure Coding book published by Liran Tal. Covers not only Node.js but also gives you another perspective on how to achieve good and secure applications, especially with understanding and handling SAST vulnerabilities. Liran - CHAPEAU!"

Eli (Tom) Lelonek
Application Security Manager at Allot
"Got my copy of Node.js secure coding! I already know I'll learn a lot 🔥"

Marco Ippolito
Node.js Collaborator & Developer Experience Engineer @NearForm
"A very interesting book that I recommend if you are in the Node.js world is "Node.js Secure Coding" by Liran Tal. Laid out with explanations, examples and tips. Warmly recommended."

Diego Betto
Founder & Senior Fullstack Developer
"Read trough first 3 chapters last night, nice work Liran!"

Aranđel Šarenac
12+ years developer, focusing on Identity Security
"Highly recommend Liran Tal's ebooks for any Node developers who are serious about security (which should be all of you!)"

Alicia Sykes
Principal Engineer @AND Digital
"Started reading the Prevention and Exploitation of Path Traversal and I am very happy with the quality. It is connecting me to some knowledge I had from working in AV company and now with code, very interesting."

Yana Ifraimov
NOC Engineer @Skai
"Node.js security rock-star Liran Tal drops another book on how to ship safe Node.js applications. I know it's hard to tell sometimes where to start from when it comes to security, as the internet is flooded with content. Well, look no more - trust content composed by Liran"

Gal Weizman
Browser JS Application Security at MetaMask & LavaMoat
"It's not every day that you can pay less than $20 for years of security wisdom. Just got this and will be using the book during my streams to improve my code."
Ray Fernando
AI app at TruthTorch.ai, ex-Apple Engineer
"The amount of content covering advanced topics in Node.js is so little, makes this a must-read"

Ruan Martinelli
Product engineer, Full-stack Freelancer & Consultant
"Outstanding book, can't wait."

Tiger Abrodi
TypeScript fanatic
"I've followed Liran Tal's work for years and definitely one of the top experts in Node.js security! Give these a look as they are essential for anyone serious about securing their Node.js applications."

Zac Rosenbauer
CTO & Co-founder at Joggr
"If you're a developer looking to better understand security vulnerabilities, this is one of the best books out there on the topic. While this book specifically focuses on Command Injection vulnerabilities in Node, the content contained within is broadly applicable to any developers writing software. It's an A++ book and absolutely worth the time to read and analyze. Liran is a top-tier security researcher and developer who's an icon in the security space. Seriously, look him up on Google, he's amazing."

Randall Degges
Head of Developer Relations & Community at Snyk
"Psyched to get my copy of Liran Tal's book: "Node.js Secure Coding: Defending Against Command Injection Vulnerabilities" Do yourself a favor and grab a copy!"

Micah Silverman
Director, DevSecOps Acceleration at Snyk
"I am just starting to read it now that I am doing security patching in Express. The book looks amazing! I mean... all the series is an amazing work, thanks a lot for investing the time to write them."

Ulises Gascón
Express TSC & Node.js Collaborator
"On point content, short book just for my liking. I like the interesting facts in the middle and code examples are good. I like the approach of Risk -> Solution -> Implementation"

Sumit Kumar
Full-Stack Engineer at Optmyzr
"This was targeted at a perfect level for me, as someone who had exposure to these topics, had done some fiddling with helmet previously in node, but this was a great succinct guide to quickly and effectively teach "what" and "why"."

Luke Rasmussen
Software Engineer
Node.js Security Modules in the Book
Introduction to Application Security
By the end of this chapter, you'll have a solid understanding of fundamental concepts in application security, including CVEs, CWEs, the OWASP Top 10, NVD, source-to-sink, and attack vectors. Gain insights into the landscape of application security organizations, laying the groundwork for a comprehensive security mindset.
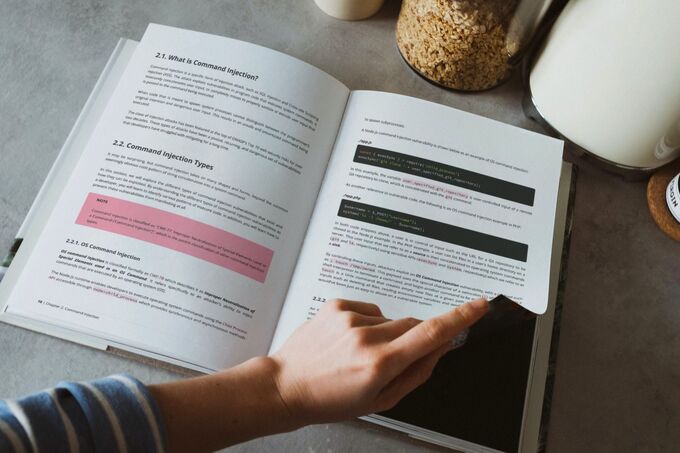
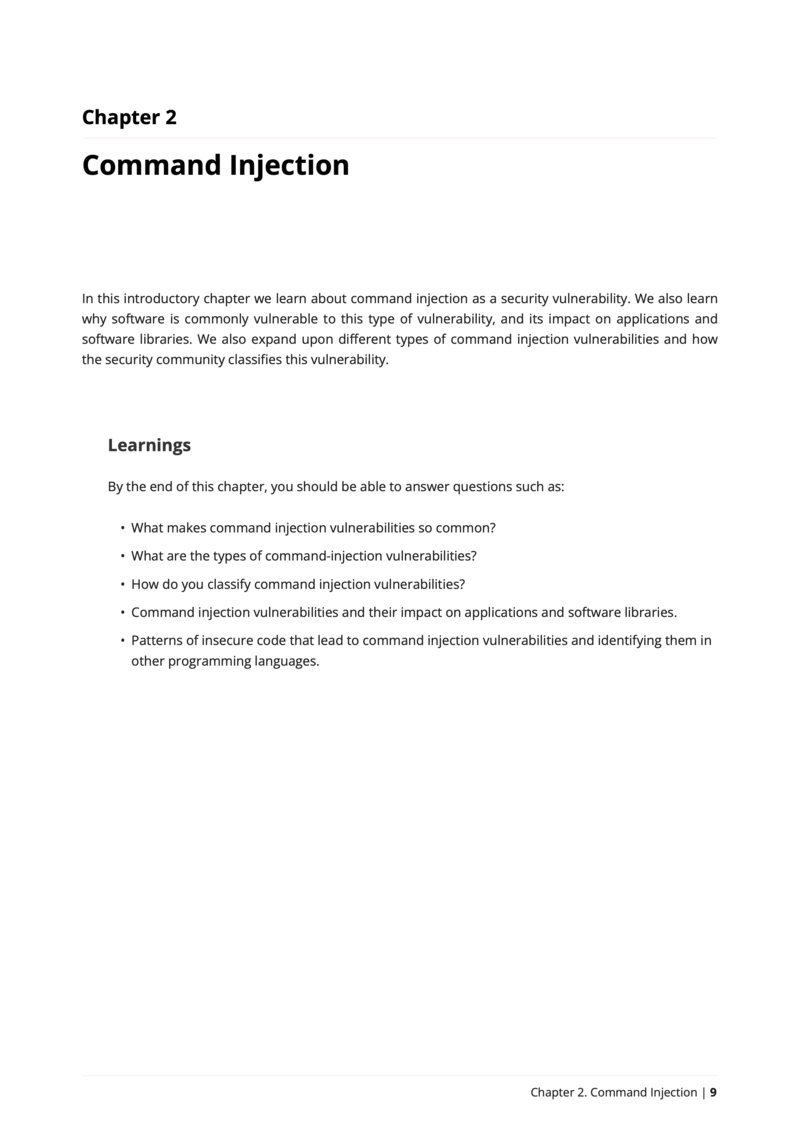
Command Injection
In this chapter, you'll delve into the world of command injection vulnerabilities, understanding their prevalence and impact. Discover the various types of command injection vulnerabilities, learning how to classify them. Explore the real-world consequences on applications and software libraries. Uncover patterns of insecure code, not only specific to Node.js but also applicable across different programming languages, empowering you to proactively identify and address such vulnerabilities
Mitigating Argument Injection in Node.js Applications
Exploring an OS Command Injection vulnerability offered a pivotal lesson in securing Node.js applications. Avoiding string concatenation for input flowing to a system command is paramount, especially when user-controlled. Despite safer alternatives like spawn() or execFile(), the insecure exec() function was used in the vulnerable code. A critical revelation was the susceptibility to argument injection, where attackers manipulate command behavior by controlling arguments. The chapter explores this attack vector and underscores effective mitigation through the strategic use of the double dash (--) to signal the end of arguments and options parsing. This learning is crucial for fortifying applications against argument injection attacks, as demonstrated in other notable cases impacting Git and Docker, providing actionable insights for developers.
Fortifying Node.js Applications Against Command Injection Threats
This chapter delves into advanced strategies for securing Node.js applications against command injection threats. Drawing insights from real-world vulnerabilities, it emphasizes the importance of meticulous examination of arguments when spawning operating system commands. The lessons learned go beyond the basics of safe system process APIs, urging developers to scrutinize command-line arguments and positional values as part of robust security controls. The chapter distills essential practices, including thorough input validation, adopting both deny-list and allow-list approaches, questioning the misconception of project popularity equating to security, advocating code review for third-party libraries, and highlighting the nuanced nature of security fixes. By internalizing these lessons, developers fortify their understanding of command injection risks, equipping them with a proactive stance in securing their Node.js applications.
Hardening Node.js Against Command Injection: Insights from vulnerable npm package
This chapter explores critical insights derived from a Command Injection vulnerability discovered in the git-promise npm package. Focusing on input validation and sanitization, the vulnerability exposed risks associated with improper handling of user input in the exec() function. Despite a prior security fix, the chapter underscores the vulnerability's persistence due to insufficient mitigation measures. An intriguing aspect is the examination of the package's popularity decline post-disclosure, emphasizing the potential impact of security incidents on a project's adoption. Developers will gain valuable knowledge on effective input validation, the limitations of common sanitization techniques, and the interconnected nature of security and project popularity. This chapter serves as a comprehensive guide to fortifying Node.js projects against Command Injection vulnerabilities, ensuring developers are equipped to navigate evolving security landscapes.
Navigating Command Injection Pitfalls in vulnerable npm package: A Technical Deep Dive
Delving into a command injection vulnerability triggered by external tool integration, this chapter unveils critical lessons for developers. The episode emphasizes the need for a deep understanding of third-party tools, exemplified by ImageMagick. The vulnerability underscores the delicate balance between convenience and security, urging developers to navigate this terrain with caution. Key takeaways include the pitfalls of relying on the exec() API and the imperative to adopt more secure alternatives like execFile(). This chapter stands as a concise guide, empowering developers to fortify their Node.js applications against similar risks and navigate the evolving landscape of secure coding.
Defending Against Command Injection: Lessons from a Strapi vulnerability
This chapter dissects the CVE vulnerability in the Strapi project, offering invaluable insights for developers navigating the intricate landscape of command injection threats. The focal point is the critical importance of input sanitization when interfacing with system commands, underscored by the Strapi scenario where a lack thereof led to remote code execution. Developers are guided to prefer secure system process APIs, steering clear of potential shell expansion pitfalls. The chapter delves into nuanced considerations, advising against invoking npm’s run-scripts directly to mitigate command injection vulnerabilities. Furthermore, it emphasizes the necessity of cautious handling of user input, especially when interfacing with sensitive API calls. By unraveling the intricacies of this real-world exploit, developers gain practical wisdom in fortifying their applications against unforeseen vulnerabilities, even in widely recognized projects like Strapi. This chapter serves as an instrumental guide for developers aiming to bolster their defenses against command injection risks.
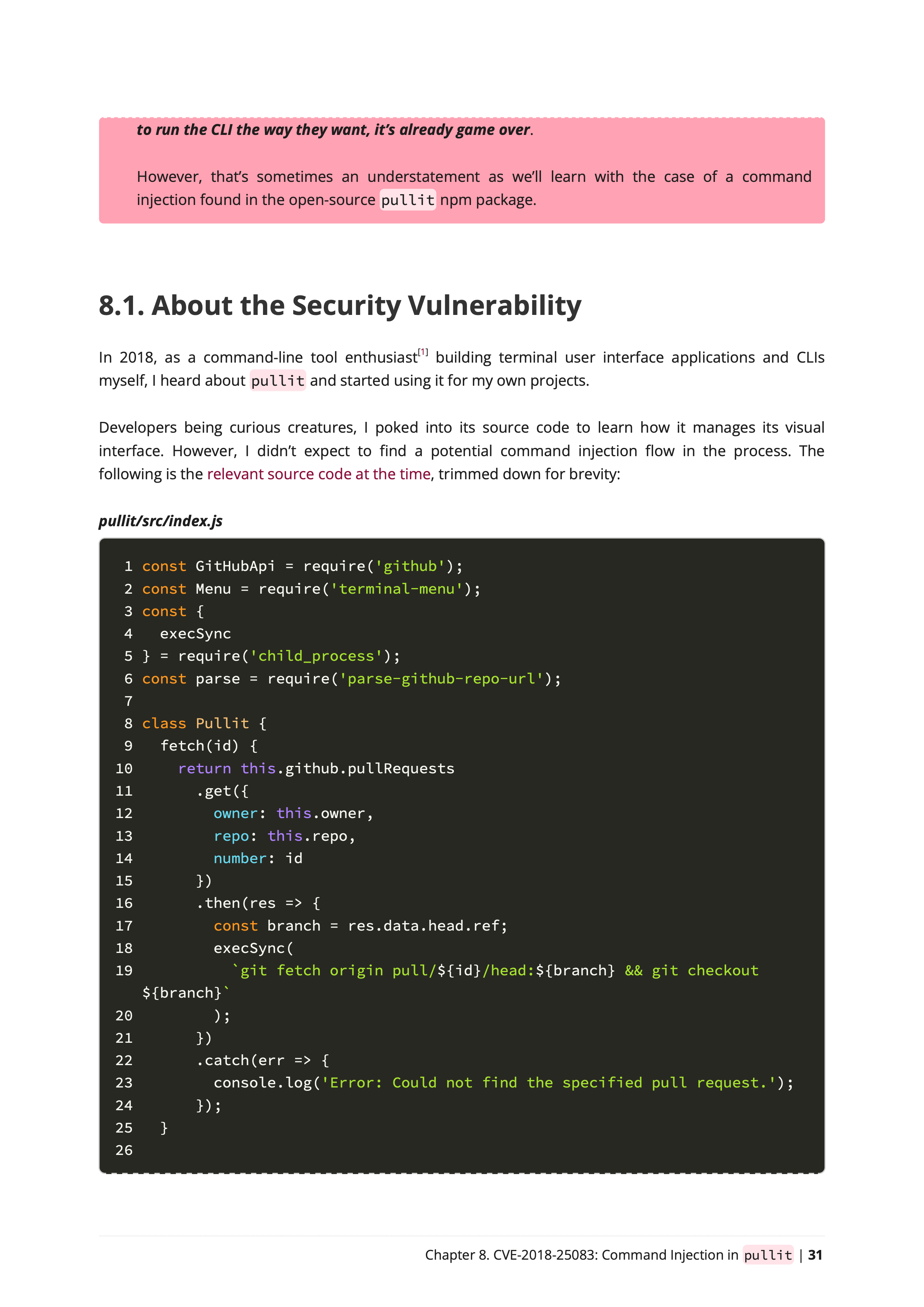
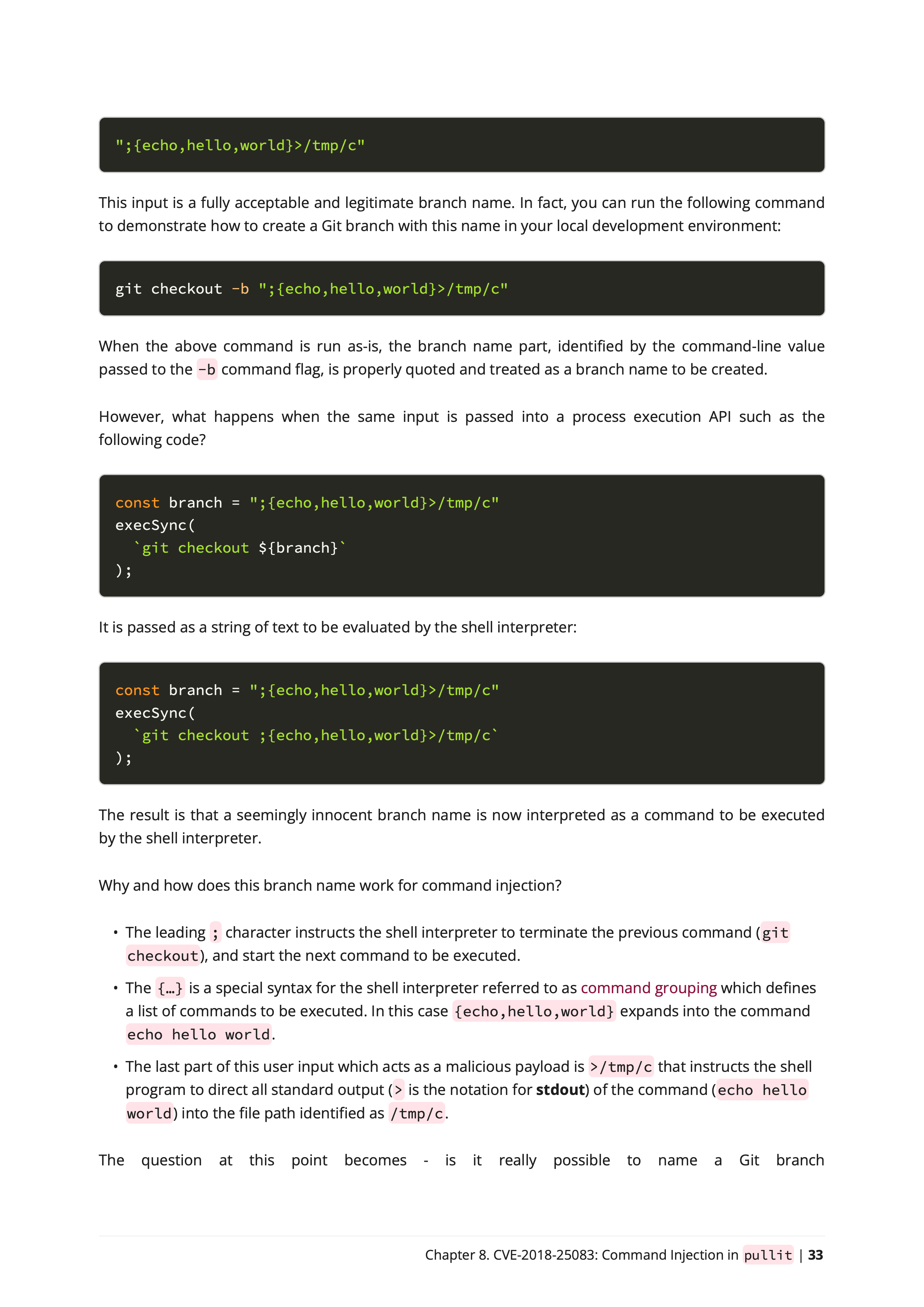
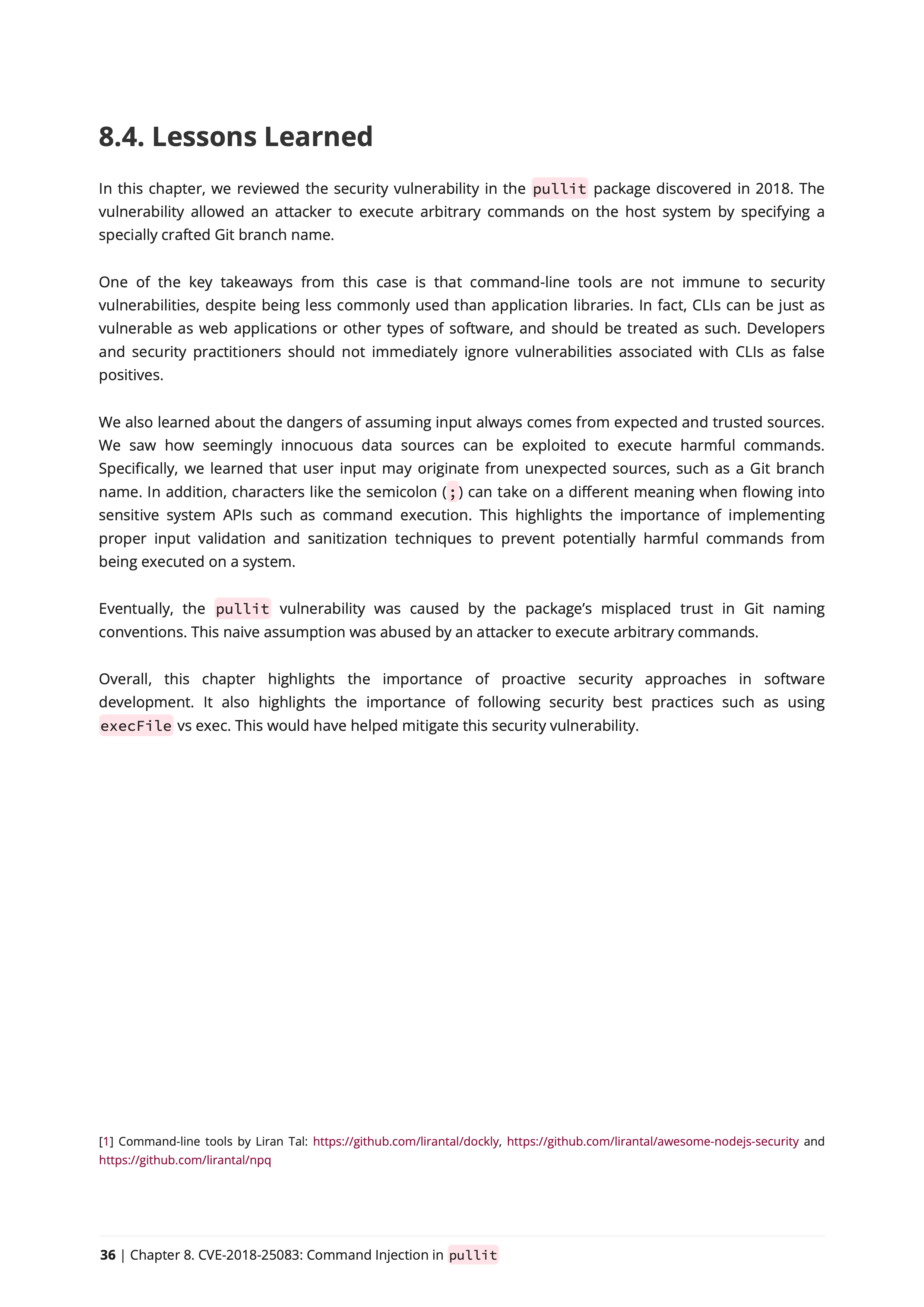
CLI Security: Leveraging GitHub as an attack vehicle against vulnerable CLIs
This chapter offers a deep dive into the security terrain, unraveling the vulnerabilities discovered in a CLI package in 2018 and how GitHub is leveraged as an attack vehicle. The key revelation is the susceptibility of command-line tools to security risks, challenging the misconception that they are inherently more secure than other software types. Developers are cautioned against dismissing CLI vulnerabilities as false positives, emphasizing the need for equal vigilance across diverse application landscapes. The narrative exposes the deceptive nature of seemingly innocuous data sources such as GitHub repositories, showcasing how unconventional origins can harbor exploitable vulnerabilities. The chapter underscores the critical role of robust input validation and sanitization practices, steering developers away from assumptions about the trustworthiness of input sources.
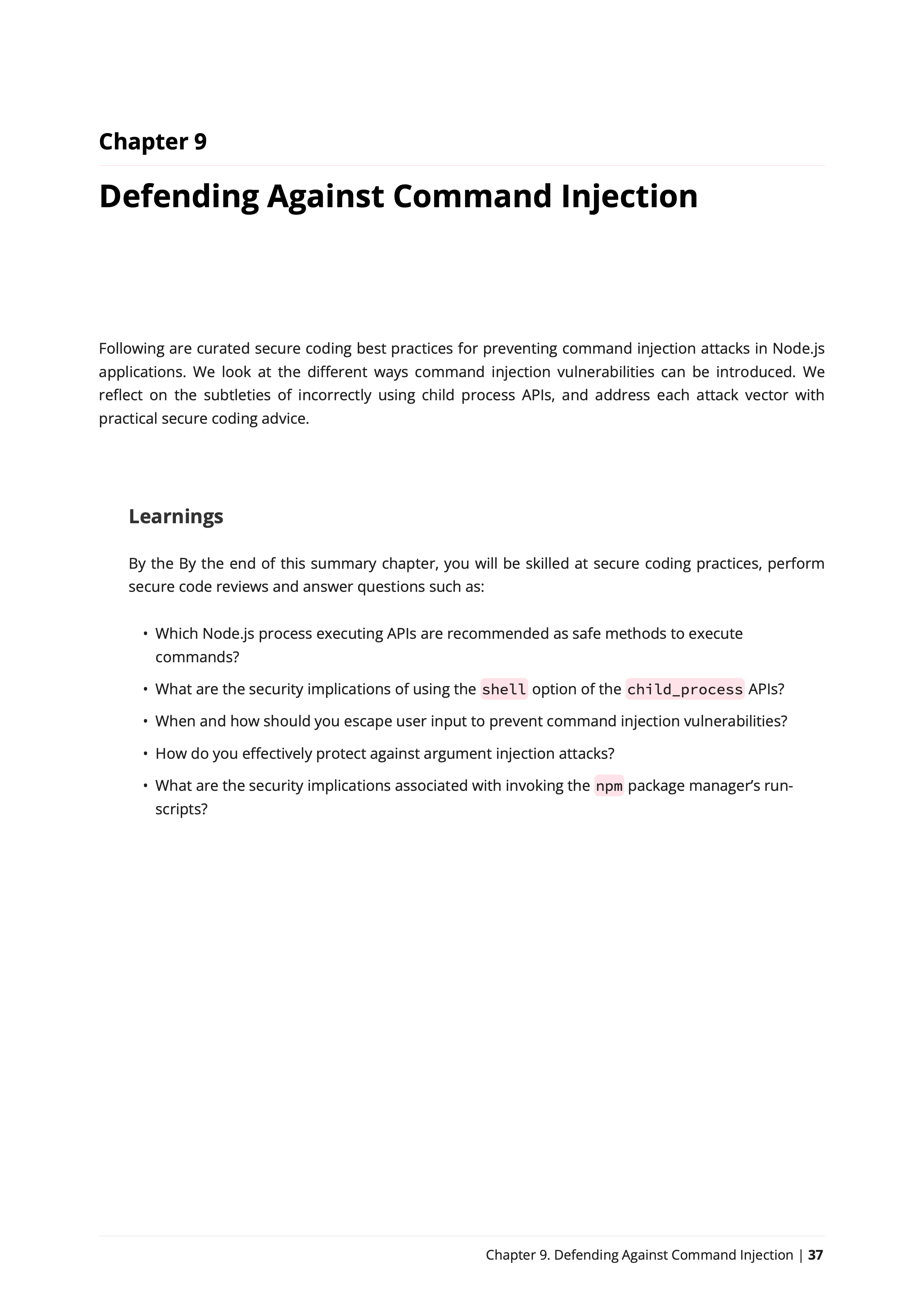
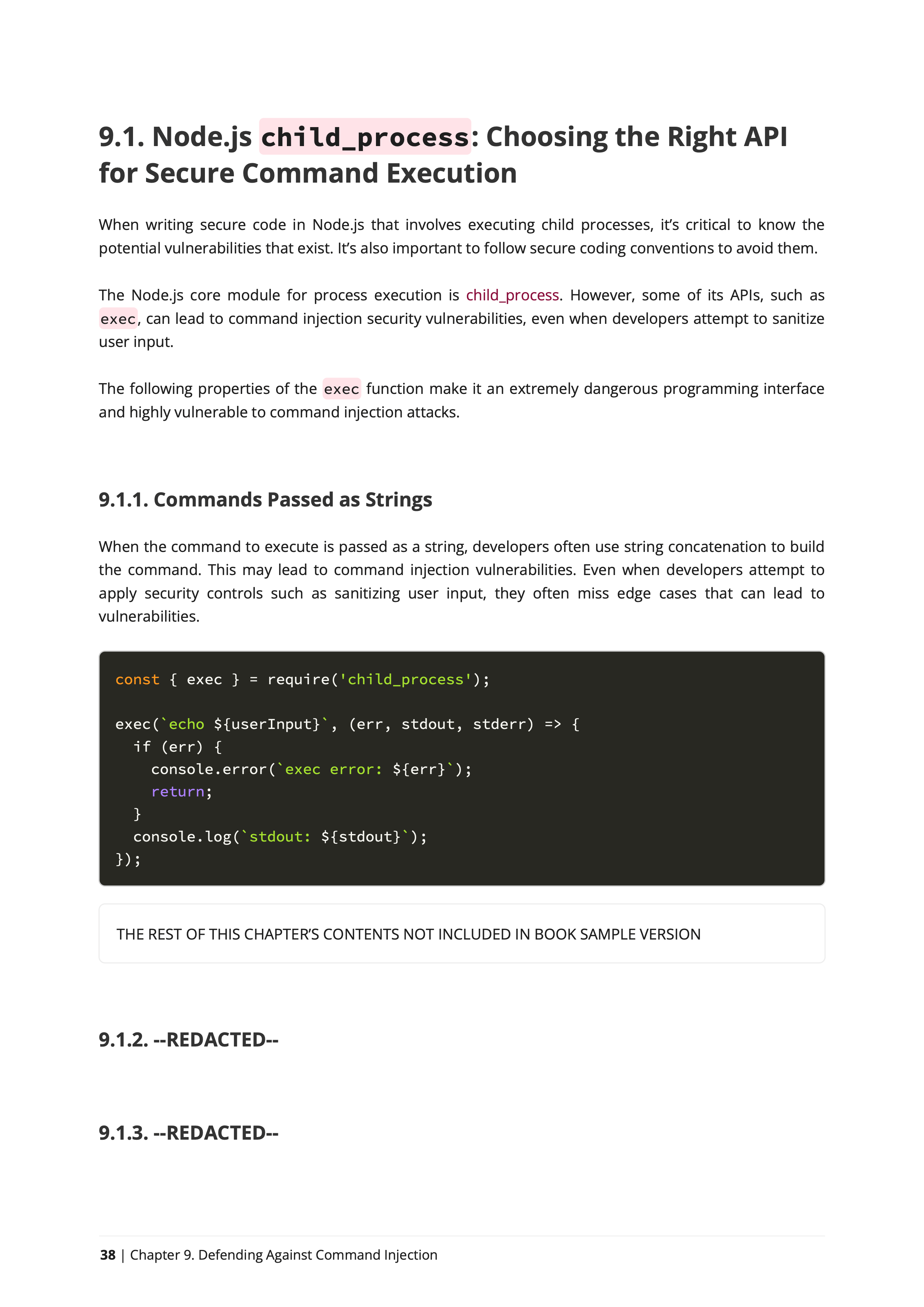
Mastering Secure Command Execution in Node.js
Dive into the intricacies of safeguarding your Node.js applications against command injection vulnerabilities with this chapter. Focusing on Node.js child_process, you'll navigate through pivotal topics like choosing the right API for secure command execution. Gain mastery over secure coding practices and code review techniques that empower you to proactively prevent command injection vulnerabilities. By the chapter's conclusion, you'll possess the skills to discern recommended Node.js process execution APIs, evaluate the security implications of utilizing the shell option in child_process APIs, implement effective user input escaping strategies, fortify defenses against argument injection attacks, and comprehend the security nuances tied to invoking npm package manager's run-scripts. This comprehensive exploration ensures you're well-equipped to tackle the multifaceted challenges of securing command execution in Node.js applications.
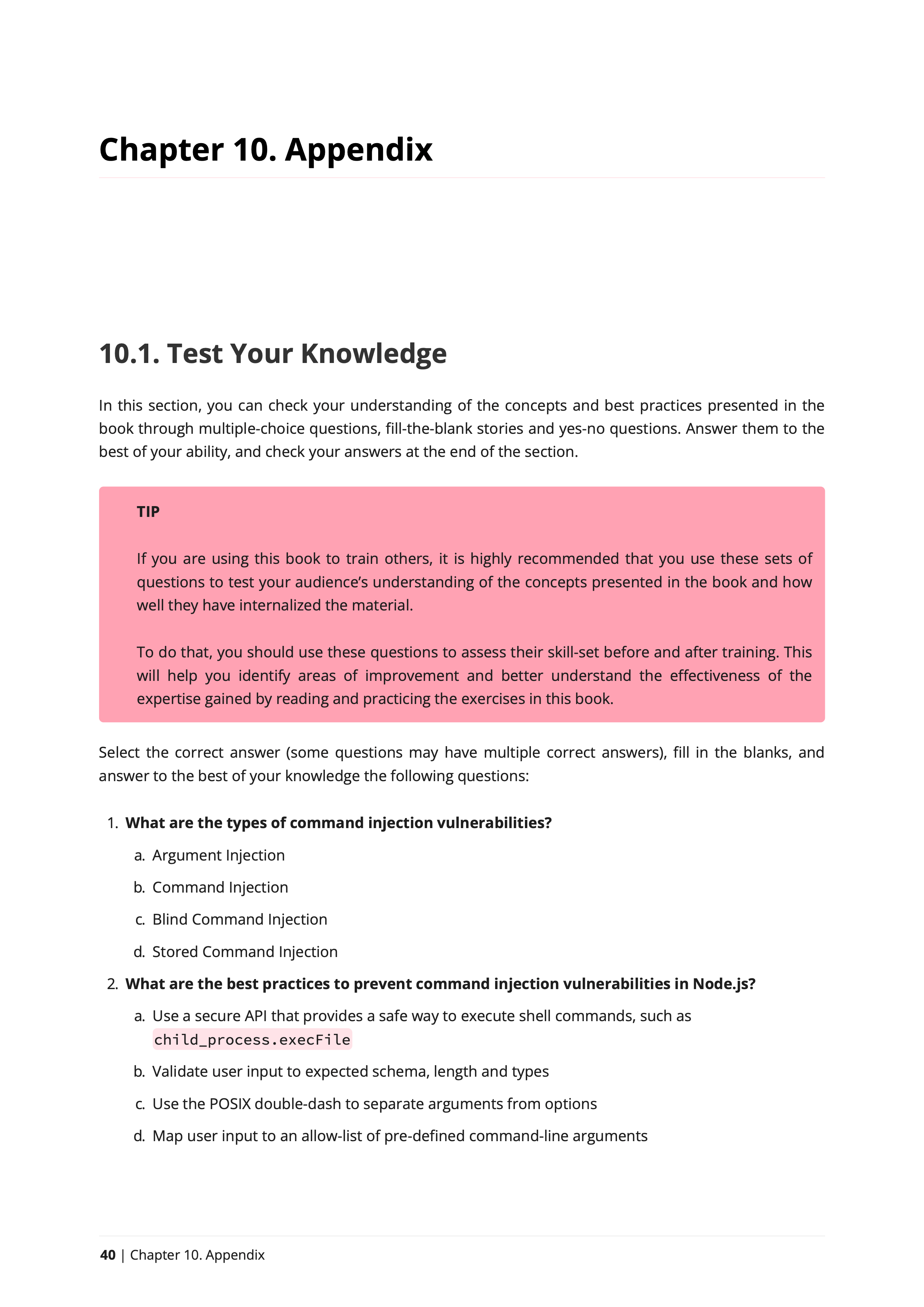
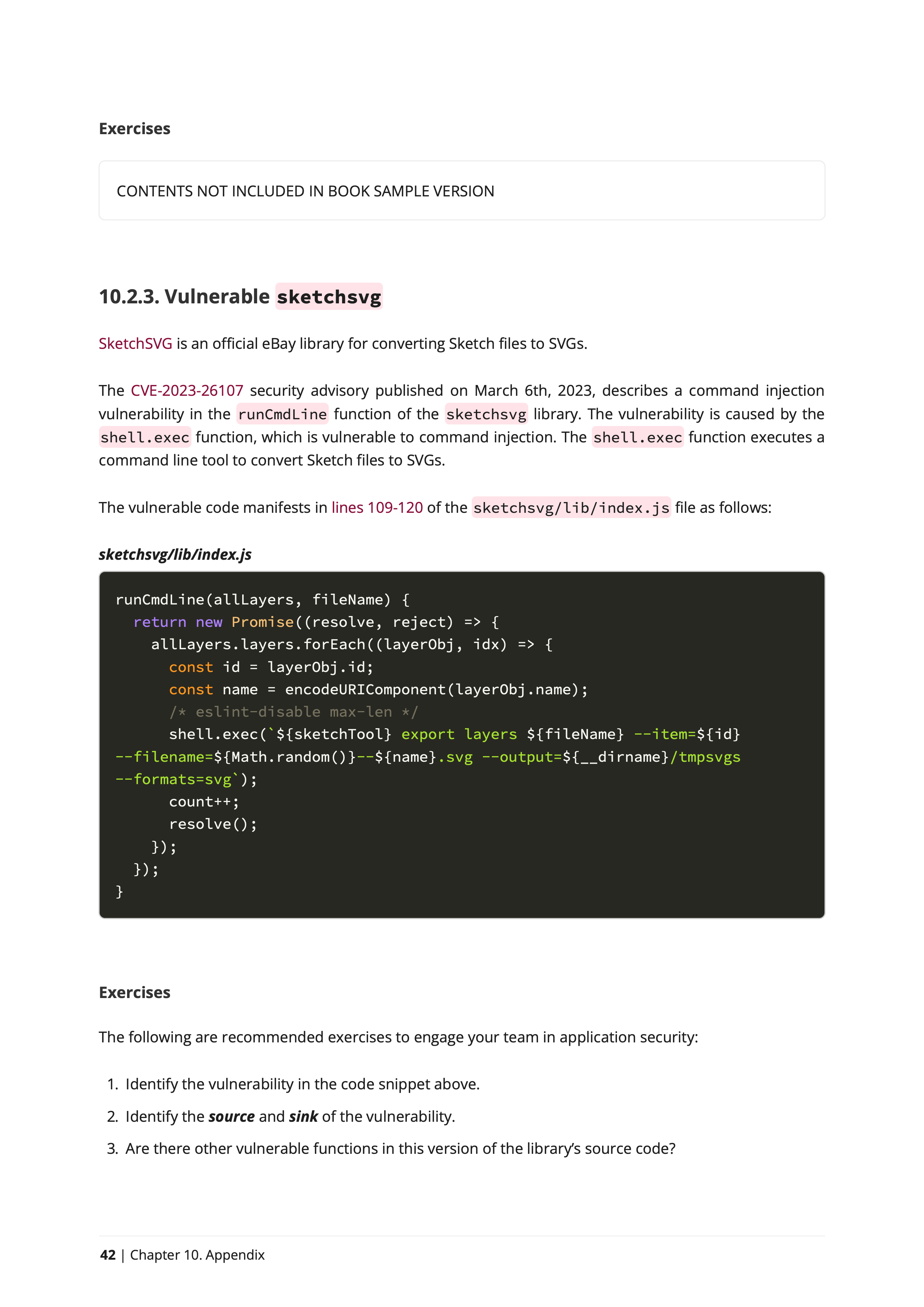
Deepening Your Command Injection Defenses
Embark on a journey to fortify your command injection defenses by delving into key topics that enhance your practical understanding. "Test Your Knowledge" invites you to assess your grasp of the presented concepts and best practices through interactive quizzes, ensuring a solid foundation. The exploration extends to "Command Injection in the Wild," offering real-world references to vulnerabilities found in both closed-source vendor software and open-source projects. These examples serve as invaluable insights, enabling you to comprehend and communicate the profound impact of command injection vulnerabilities effectively. Additionally, "CVEs in This Book" provides a comprehensive reference list, streamlining your access to critical information. This chapter serves as a pivotal resource, arming you with the knowledge and tools needed to elevate your command injection defense strategies and communicate security priorities within your organization.
Master Node.js Security Through Hands-On Learning and Best Practices
Comprehensive learning path
Whether you're a beginner or an experienced JavaScript developer, this Node.js Secure Coding book takes a comprehensive approach to security. From basic terminology to introduction to Command Injection, you'll learn about assorted patterns of insecure code observed in popular and well-known npm packages.
Hands-on learning
Unlike other security books that rely on theoretical examples, this book is based on real-world vulnerable code found in popular npm packages. You'll get hands-on experience reviewing and fixing security issues in these projects, learning practical security skills and Node.js secure coding best practices.
Best practices and practical takeaways
Each chapter ends with a summary of the lessons learned, highlighting best practices for securing your Node.js code and improving your overall security knowledge of Command Injection vulnerabilities.
Congratulations!
You've leveled up your security skills!

Liran is a tireless advocate for security in the JS ecosystem. He works hard to build bridges, educate developers about security issues, and support Open Source projects working to improve their security posture. Liran has served on the Node security team and is always available to support developers!
by the OpenJS Foundation
Elevated Reading Experience
Who said books don't need to look good?
Forget boring black and white, ceremonial typeface and scientific-like book formatting.
With an elegant color palette, thoughtful formatting, and carefully chosen fonts, you'll enjoy a unique reading experience. Every page is designed to help you focus on the content and immerse yourself in the learning journey. Get ready to elevate your reading experience.
Beautiful Color Palette
Everything from the book's cover design to notes, code blocks, typography styles and notes has been designed with a color palette that is unique and specially crafted for this book.
Beautifully Rendered Code Blocks
You'll read a lot of code.
More precisely, you will read a lot of vulnerable code.
To make the source code review process as fluent as possible, code blocks are styled with the rogue
source highlighter using the base16.monokai.dark
theme. This is to provide an effective color contrast.
Node.js Security Learnings
Chapters start with a short introduction to the topic, citing key areas of new knowledge gained, and end with a summary and lessons learned.
Master Node.js Security:
Get Started with Secure Coding
The Definitive Guide to Defending Against Command Injection Vulnerabilities and Building Secure Node.js Applications
Developers Level Up
- Access an introduction to AppSec and Command Injection
- 6 chapters reviewing vulnerable npm packages
- Real-world CVE analysis of vulnerable code
- Experience hands-on defensive programming approach
- Command Injection attack and defense secure coding
- Best practices for securing Node.js code
Security Analyst for the Node.js Foundation
In his role as a security analyst in the Node.js Foundation's Security Working Group, Liran reviewed hundreds of vulnerability reports for npm packages and established processes for responsible security disclosures and vulnerability triage 🏴☠️.
Education is a core practice
Passionate about educating developers on application security and secure coding practices, Liran is a world-wide international speaker, workshop instructor, and author of several books on the subject. He occasionally speaks on software security topics at academic institutions, such as presenting to students at the Electrical and Computer Engineering School at Purdue University 🎓.
Award-winning GitHub Star ⭐️
Liran received the GitHub Star recognition award from GitHub for his work educating and inspiring developers and actively advocating for web security.
Recipient of the Pathfinder for Security Award 🎖️
Honored by the OpenJS Foundation with the Pathfinder for Security Award, Liran is recognized for his work advancing Node.js security.
I'm a Security Researcher
An accomplished security researcher, Liran has disclosed security vulnerabilities in various open source software projects, including being credited with CVEs to his name for vulnerabilities in npm packages with millions of downloads.
Acclaimed Recognition at Black Hat
Liran's discovery in supply chain security research, including Lockfile Injection, was presented at the prestigious Black Hat Europe 2021 cybersecurity conference. Liran is also the creator of several developer security tooling projects such as npq, is-website-vulnerable, and snync, which help developers and enterprises defend against dependency confusion attacks.
About Liran Tal
Liran Tal is an accomplished software developer, respected security researcher, and prominent advocate for open source software in the JavaScript community. As an experienced author and educator, Liran has written several widely respected books on software security. These include "Serverless Security" published by O'Reilly, as well as the self-published titles "Essential Node.js Security" and "Web Security: Learning HTTP Security Headers". Liran's leadership in open source security includes significant contributions to OWASP projects, recording supply chain security incidents at the CNCF, and various OpenSSF initiatives. Currently, Liran is a developer advocate at Snyk where he empowers developers with the knowledge and tools needed to build and deploy secure software.
Frequently Asked Questions
Will I learn Node.js security best practices?
I wrote this book first and foremost as a Node.js coding best practices so you can apply secure coding conventions. You can think of it as a Node.js security checklist that you can apply at work or in your own projects.
Will I learn about Node.js security vulnerabilities?
Yes, more than you realized. Forget common Node.js security tutorials and generic security guides - experience true security expertise with this hands-on approach that will analyze actual npm packages that were found vulnerable, some of which you may use today in your projects, and learn why they were vulnerable and how to fix insecure code.
What programming level is required to benefit from this book?
This book doesn't assume any prior knowledge of security nor advanced knowledge of Node.js. It opens with a short introduction to application security, then to Command Injection class of vulnerabilities, and continues to deep-dive into publicly-known vulnerable npm package versions. You will read a lot of code and learn why it's insecure, and how to fix it.
Can it help with Node.js API security?
Probably. As a backend developer, you may need to resort to process execution APIs such as exec() or spawn() in order to perform image processing off the main thread, or other use-cases. You will learn how to secure your Node.js APIs in reference to preventing common Command Injection pitfalls and insecure coding.
Can I contact the author for additional help or questions?
Yes, anytime. I'm always happy to help! Reach out to me here [liran at lirantal dot com].
Does this book focus on other secure Node.js aspects?
No, it focuses specifically and entirely on Command Injection vulnerabilities and how to prevent them. Regardless, it will likely teach you about application security topics and Node.js security best practices that you can apply in your own projects.
Hands-On Node.js Security
Master secure coding in Node.js with real-world vulnerable dependencies and experience secure coding firsthand