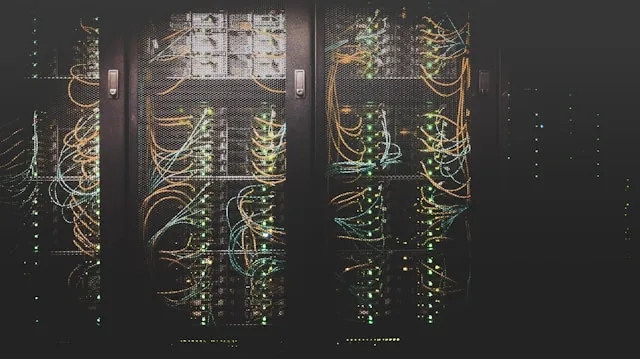
SSRF Shenanigans in safe-axios: Redirects Open the Backdoor
Dive into the intricacies of a critical SSRF vulnerability in `safe-axios`, a popular npm package designed to protect against SSRF attacks. Learn how attackers exploit redirects to bypass security measures and access unauthorized resources.